دوره های آموزشی امنیت شبکه در جونیپر شامل دو بخش می باشد; بخش اول مربوط به فایروال های جونیپر با سیستم عامل net screen و بخش دوم مربوط به فایروال های جونیپر با سیستم عامل Junos مربوط به سری SRX می باشد. با توجه به اینکه تقاضای برگزاری دوره های جونیپر سری SRX بیشتر می باشد، در این مستند دوره های آموزشی جونیپر به همراه سیلابس دوره ها آورده شده است.
همانطور که مستحضر هستید فایروال های امنیتی جونیپر از بهترین فایروال های امنیتی جهان می باشد و در حال حاضر نیز استفاده از فایروال های جونیپر در بسیاری از سازمان های دولتی و خصوصی مورد استفاده قرار می گیرد، دانشجویان این دوره علاوه بر آشنایی با مفاهیم مختلف امنیت شبکه و پیکر بندی فایروال جونیپر، با انواع روش های جلوگیری از نفوذ به شبکه های کامپیوتری آشنا خواهند شد.
دوره های آموزشی جونیپر از زیر شاخه امنیت شبکه می باشد، در این دوره ۵۰% مفاهیم امنیت شبکه به صورت کاربردی ذکر می شود و ۵۰% مربوط به موارد پیکربندی تجهیزات فایروال جونیپر سری SRX می باشد.
مدارک و دوره های جونیپر سری SRX
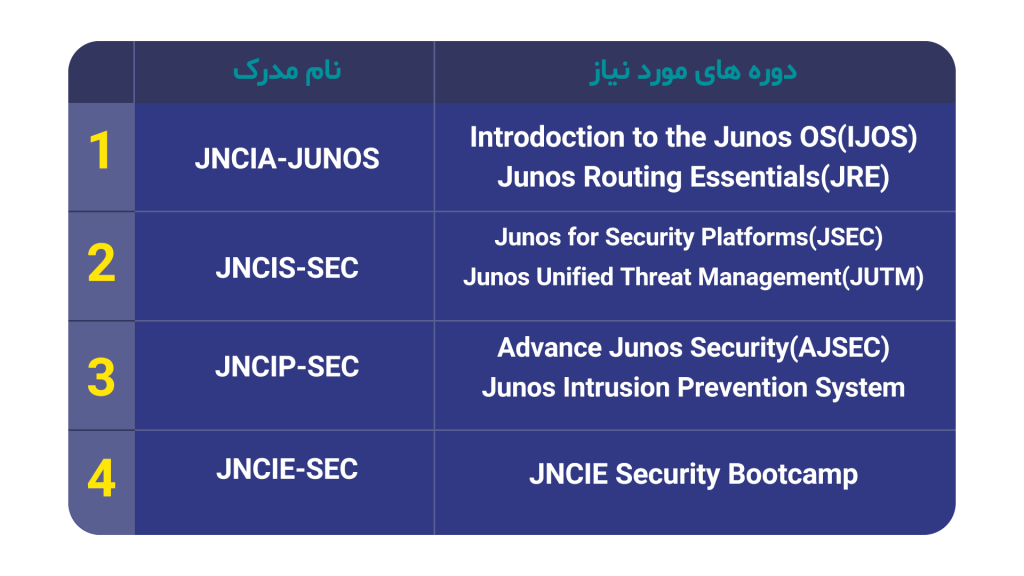
دانشجویان دوره امنیت شبکه فایروال های جونیپر، جهت گذراندن دوره، کسب دانش و توانمندی های فنی این دوره می بایست چهار مدرک اصلی مربوط به این دوره ها را کسب نمایند. مدارک به ترتیب شامل لیست زیر می باشد:
1. JNCIA-JUNOS
2. JNCIS-SEC
3. JNCIP-ENT
4. JNCIA-SEC
اما لازم به ذکر است جهت کسب هر کدام از مدارک اشاره شده می بایست دوره هایی طی شود. لیست جدول زیر نشان گر دوره های مرتبط به هر کدام از این دوره ها می باشد.
لیست دوره ها و مدارک دوره امنیت شبکه در فایروال های جونیپر سری SRX
دوره JNCIA برای افرادی که قصد دارند در بخش پیکربندی و عیب یابی دستگاه های SRX فعالیت کنند بسیار مناسب است. این دوره به افراد کمک می کند تا بتوانند با ساختار Junos OS آشنایی کامل پیدا کنند و در این حوزه فعالیت کنند.
دوره Introduction to the Junos Operating System (IJOS)
Objectives
After successfully completing this course, you should be able to:
- Describe the basic design architecture of the Junos OS.
- Identify and provide a brief overview of Junos devices.
- Navigate within the Junos CLI.
- Perform tasks within the CLI operational and configuration modes.
- Restore a Junos device to its factory-default state.
- Perform initial configuration tasks.
- Configure and monitor network interfaces.
- Describe user configuration and authentication options.
- Perform secondary configuration tasks for features and services such as system logging (syslog) and tracing, Network Time Protocol (NTP), configuration archival, and SNMP.
- Monitor basic operation for the Junos OS and devices.
- Identify and use network utilities.
- Upgrade the Junos OS.
- Perform file system maintenance and password recovery on a Junos device.
- Navigate within the Junos J-Web interface.
Course Contents
Day 1
Chapter 1: Course Introduction
Chapter 2: Junos Operating System Fundamentals
- The Junos OS
- Traffic Processing
- Platforms Running the Junos OS
Chapter 3: User Interface Options
- User Interface Options
- The Junos CLI: CLI Basics
- The Junos CLI: Operational Mode
- The Junos CLI: Configuration Mode
- Lab 1: The Junos CLI
Chapter 4: Initial Configuration
- Factory-Default Configuration
- Initial Configuration
- Interface Configuration
- Lab 2: Initial System Configuration
Chapter 5: Secondary System Configuration
- User Configuration and Authentication
- System Logging and Tracing
- Network Time Protocol
- Archiving Configurations
- SNMP
- Lab 3: Secondary System Configuration
Chapter 6: Operational Monitoring and Maintenance
- Monitoring Platform and Interface Operation
- Network Utilities
- Maintaining the Junos OS
- Password Recovery
- Lab 4: Operational Monitoring and Maintenance
Appendix A: Interface Configuration Examples
- Review of the Interface Configuration Hierarchy
- Interface Configuration Examples
- Using Configuration Groups
Appendix B: The J-Web Interface
- The J-Web GUI
- Configuration
- Lab 5 (Optional): The J-Web Interface
دوره Junos Routing Essentials (JRE)
Objectives
After successfully completing this course, you should be able to:
- Explain basic routing operations and concepts.
- View and describe routing and forwarding tables.
- Configure and monitor static routing.
- Configure and monitor OSPF.
- Describe the framework for routing policy.
- Explain the evaluation of routing policy.
- Identify instances where you might use routing policy.
- Write and apply a routing policy.
- Describe the framework for firewall filters.
- Explain the evaluation of firewall filters.
- Identify instances where you might use firewall filters.
- Write and apply a firewall filter.
- Describe the operation and configuration for unicast reverse path forwarding (RPF).
Course Contents
Day 1
Chapter 1: Course Introduction
Chapter 2: Routing Fundamentals
- Routing Concepts: Overview of Routing
- Routing Concepts: The Routing Table
- Routing Concepts: Routing Instances
Static Routing
- Dynamic Routing
- Lab 1: Routing Fundamentals
Chapter 3: Routing Policy
- Routing Policy Overview
- Case Study: Routing Policy
- Lab 2: Routing Policy
Chapter 4: Firewall Filters
- Firewall Filters Overview
- Case Study: Firewall Filters
- Unicast Reverse-Path-Forwarding Checks
- Lab 3: Firewall Filters
Appendix A: Class of Service
- CoS Overview
- Traffic Classification
- Traffic Queuing
- Traffic Scheduling
- Case Study: CoS
- Lab 4: Class of Service (Optional)
دوره JNCIS-SEC نیز می تواند متخصصانی در سطح حرفه ای برای کار با دستگاه های SRX را روانه بازار کار کند. این متخصصان با دانش و تجربه بالاتری در زمینه امنیت مربوط به سیستم عامل juniper قادر خواهند بود که در سطوح بالاتری از ساختار security فعالیت داشته باشند.
دوره Junos Security (JSEC)
Objectives
After successfully completing this course, you should be able to:
- Describe traditional routing and security and the current trends in internetworking.
- Provide an overview of SRX Series devices and software architecture.
- Describe the logical packet flow and session creation performed by SRX Series devices.
- Describe, configure, and monitor zones.
- Describe, configure, and monitor security policies.
- Describe, configure, and monitor firewall user authentication.
- Describe various types of network attacks.
- Configure and monitor Screen options to prevent network attacks.
- Explain, implement, and monitor NAT, as implemented on Junos security platforms.
- Explain the purpose and mechanics of IP Security (IPsec) virtual private networks (VPNs).
- Implement and monitor policy-based and route-based IPsec VPNs.
- Utilize and update the IDP signature database.
- Configure and monitor IDP policy with policy templates.
- Describe, configure, and monitor high availability chassis clusters.
Course Contents
Day 1
Chapter 1: Course Introduction
Chapter 2: Introduction to Junos Security
- Traditional Routing
- Traditional Security
- The Junos OS Architecture
Chapter 3: Zones
- The Definition of Zones
- Zone Configuration
- Monitoring Security Zones
- Lab 1: Configuring and Monitoring Zones
Chapter 4: Security Policies
- Security Policy Overview
- Junos ALGs
- Policy Components
- Verifying Policy Operation
- Policy Scheduling and Rematching
- Policy Case Study
- Lab 2: Security Policies
Day 2
Chapter 5: Firewall User Authentication
- Firewall User Authentication Overview
- Pass-Through Authentication
- Web Authentication
- Client Groups
- Using External Authentication Servers
- Verifying Firewall User Authentication
- Lab 3: Configuring Firewall Authentication
Chapter 6: Screen Options
- Multilayer Network Protection
- Stages and Types of Attacks
- Using Junos Screen Options—Reconnaissance Attack Handling
- Using Junos Screen Options—Denial of Service Attack Handling
- Using Junos Screen Options—Suspicious Packets Attack Handling
- Applying and Monitoring Screen Options
- Lab 4: Implementing Screen Options
Chapter 7: Network Address Translation
- NAT Overview
- Source NAT Operation and Configuration
- Destination NAT Operation and Configuration
- Static NAT Operation and Configuration
- Proxy ARP
- Monitoring and Verifying NAT Operation
- Lab 5: Network Address Translation
Day 3
Chapter 8: IPsec VPNs
- VPN Types
- Secure VPN Requirements
- IPsec Details
- Configuration of IPsec VPNs
- IPsec VPN Monitoring
- Lab 6: Implementing IPsec VPNs
Chapter 9: Introduction to Intrusion Detection and Prevention
- Introduction to Junos IDP
- IDP Policy Components and Configuration
- Signature Database
- Case Study: Applying the Recommended IDP Policy
- Monitoring IDP Operation
- Lab 7: Implementing IDP
Chapter 10: High Availability Clustering Theory
- High Availability Overview
- Chassis Cluster Components
- Advanced Chassis Cluster Topics
Chapter 11: High Availability Clustering Implementation
- Chassis Cluster Operation
- Chassis Cluster Configuration
- Chassis Cluster Monitoring
- Lab 8: Implementing High Availability Techniques
Appendix A: SRX Series Hardware and Interfaces
- Branch SRX Platform Overview
- High End SRX Platform Overview
- SRX Traffic Flow and Distribution
- SRX Interfaces
دوره Junos Unified Threat Management (JUTM)
Objectives
After successfully completing this course, you should be able to:
- Describe the challenges that branch offices present to network managers.
- List the major features that UTM offers.
- Explain how each major feature addresses the challenges of the branch office.
- List the SRX Series Services Gateways hardware devices on which UTM is available.
- Describe the UTM features that require specific licenses.
- Define terms used in the creation of effective antispam UTM policies.
- Describe the process by which UTM examines traffic for spam.
- Describe the overall process of configuring an antispam UTM policy.
- Describe the kinds of information available from the device when it has detected spam.
- Describe how the AV process examines traffic.
- Describe the differences between full file-based AV versus express AV.
- Describe the settings that are required for configuring AV protection.
- Explain how these settings affect scanning performance and effectiveness.
- Describe options available for scanning supported protocols.
- List the general steps required to configure AV.
- Describe the statistical information available to verify AV functionality.
- Describe content and Web filtering and their purpose.
- List and describe each of the parameters used when configuring Web and content filtering.
- Describe in general terms the steps necessary to configure web and content filtering.
- Monitor Web and content filtering.
Course Contents
Chapter 1: Course Introduction
Chapter 2: UTM Overview
- Branch Office Challenges
- UTM Feature Overview
- Design Basics
- Hardware Support
- Licensing of Features
- Lab 1: Connecting to the Lab Equipment and Testing Connectivity
Chapter 3: Antispam
- Antispam Terminology
- Overview of Antispam Process
- UTM Policy Overview
- Configuration Steps
- Monitoring Antispam
- Lab 2: Configuring an Antispam Policy
Chapter 4: Full File-Based and Express Antivirus
- Antivirus Terminology
- Overview of Antivirus Process
- AV Operation
- Full File-based AV Configuration
- Express AV Configuration
- Monitoring AV
- Lab 3: Antivirus Configuration and Testin
Chapter 5: Content and Web Filtering
- Overview and Terminology
- Configuration
- Verification and Monitoring
- Lab 4: Configuring Content and Web Filtering
دوره JNCIP برای متخصصان فناوری اطلاعات با دانش و تجربه پیشرفته در زمینه امنیت و مرتبط به ساختار Juniper می باشد. با گذراندن این دوره به یک فرد حرفه ای تبدیل می شوید و قادر خواهید بود در سطح پیشرفته با دستگاه های SRX در زمینه های امنیتی فعالیت داشته باشید.
دوره Advanced Junos Security (AJSEC)
Objectives
After successfully completing this course, you should be able to:
- Demonstrate understanding of concepts covered in the prerequisite Junos Security course.
- Describe the various forms of security supported by the Junos OS.
- Implement features of the AppSecure suite, including AppID, AppFW, and AppTrack.
- Configure custom application signatures.
- Describe Junos security handling at Layer 2 versus Layer 3.
- Implement Layer 2 transparent mode security features.
- Demonstrate understanding of Logical Systems (LSYS).
- Implement address books with dynamic addressing.
- Compose security policies utilizing ALGs, custom applications, and dynamic addressing for various scenarios.
- Use Junos debugging tools to analyze traffic flows and identify traffic processing patterns and problems.
- Describe Junos routing instance types used for virtualization.
- Implement virtual routing instances.
- Describe and configure route sharing between routing instances using logical tunnel interfaces.
- Describe and implement static, source, destination, and dual NAT in complex LAN environments.
- Describe and implement variations of persistent NAT.
- Describe and implement Carrier Grade NAT (CGN) solutions for IPv6 NAT, such as NAT64, NAT46, and DS-Lite.
- Describe the interaction between NAT and security policy.
- Demonstrate understanding of DNS doctoring.
- Differentiate and configure standard point-to-point IP Security (IPsec) virtual private network (VPN) tunnels, hub-and-spoke VPNs, dynamic VPNs, and group VPNs.
- Implement IPsec tunnels using virtual routers.
- Implement OSPF over IPsec tunnels and utilize generic routing encapsulation (GRE) to interconnect to legacy firewalls.
- Monitor the operations of the various IPsec VPN implementations.
- Describe public key cryptography for certificates.
- Utilize Junos tools for troubleshooting Junos security implementations.
- Perform successful troubleshooting of some common Junos security issues.
Course Contents
Day 1
Chapter 1: Course Introduction
Chapter 2: AppSecure
- AppSecure Overview
- AppID
- AppTrack
- AppFW
- AppDoS
- AppQoS
- Lab 1: Implementing AppSecure
Chapter 3: Junos Layer 2 Packet Handling and Security Features
- Transparent Mode Security
- Layer 2 Ethernet Switching
- Lab 2: Implementing Layer 2 Security
Chapter 4: Virtualization
- Virtualization Overview
- Routing Instances
- Logical Systems
- Lab 3: Implementing Junos Virtual Routing
Day 2
Chapter 5: Advanced NAT Concepts
- Operational Review
- NAT: Beyond Layer 3 and Layer 4 Headers
- DNS Doctoring
- IPv6 NAT
- Advanced NAT Scenarios
- Lab 4: Advanced NAT Implementations
Chapter 6: IPsec Implementations
- Standard VPN Implementations Review
- Public Key Infrastructure
- Hub-and-Spoke VPNs
- Lab 5: Hub-and-Spoke IPsec VPNs
Day 3
Chapter 7: Enterprise IPsec Technologies: Group and Dynamic VPNs
- Group VPN Overview
- GDOI Protocol
- Group VPN Configuration and Monitoring
- Dynamic VPN Overview
- Dynamic VPN Implementation
- Lab 6: Configuring Group VPNs
Chapter 8: IPsec VPN Case Studies and Solutions
- Routing over VPNs
- IPsec with Overlapping Addresses
- Dynamic Gateway IP Addresses
- Enterprise VPN Deployment Tips and Tricks
- Lab 7: Implementing Advanced IPsec VPN Solutions
Chapter 9: Troubleshooting Junos Security
- Troubleshooting Methodology
- Troubleshooting Tools
- Identifying IPsec Issues
- Lab 8: Performing Security Troubleshooting Techniques
Appendix A: SRX Series Hardware and Interfaces
- Branch SRX Platform Overview
- High End SRX Platform Overview
- SRX Traffic Flow and Distribution
- SRX Interfaces
Junos Intrusion Prevention Systems (JIPS) دوره
Objectives
After successfully completing this course, you should be able to:
- Explain the terms and concepts related to intrusion prevention.
- Describe general types of intrusions and network penetration steps.
- Explain how scanning can be used to gather information about target networks.
- Define and describe the terminology that comprises Juniper Networks IPS functionality.
- Describe the basic functions and features available on the SRX Series platform that provide IPS functionality.
- Describe how to access the SRX Series Services Gateways with IPS functionality for configuration and management.
- Describe the steps that the IPS engine takes when inspecting packets.
- Configure the SRX Series Services Gateways for IPS functionality.
- Describe the components of IPS rules and rulebases.
- Configure an IPS exempt rule.
- Explain the types of signature-based attacks.
- Configure a custom signature attack object.
- Describe the uses of custom signatures and how to configure them.
- Describe commonly used evasion techniques and how to block them.
- Explain the mechanisms available on the SRX Series Services Gateway to detect and block DoS and DDoS attacks.
- Configure screens to block IP spoofing and SYN flooding.
- Describe additional security flow protection mechanisms.
- Demonstrate how the SRX Series device performs TCP SYN checking.
- Explain the STRM capabilities for capturing, logging, and reporting network traffic.
- Describe the logging and reporting capabilities available for SRX IP functionality within STRM.
Course Contents
Day 1
Chapter 1: Course Introduction
Chapter 2: Introduction to Intrusion Prevention Systems
- Network Asset Protection
- Intrusion Attack Methods
- Intrusion Prevention Systems
- IPS Traffic Inspection Walkthrough
Chapter 3: IPS Policy and Initial Configuration
- SRX IPS Requirements
- IPS Operation Modes
- Basic IPS Policy Review
- Basic IPS Policy Lab
Chapter 4: IPS Rulebase Operations
- Rulebase Operations
- IPS Rules
- Terminal Rules
- IP Actions
- Configuring IPS Rulebases Lab
Day 2
Chapter 5: Custom Attack Objects
- Predefined Attack Objects
- Custom Attack Objects
- Fine-Tuning the IPS Policy
- Custom Signatures Lab
Chapter 6: Additional Attack Protection Mechanisms
- Scan Prevention
- Blocking Evasion and DoS Attacks
- Security Flow Protection Mechanisms
- Security Flow Protection Mechanisms Lab
Chapter 7: IPS Logging and Reporting
- Junos Syslog and Operational Commands
- STRM IPS Logging
- IPS Logging Lab
Juniper Networks Certified Expert: Security (JNCIE-SEC)
این دوره برای تایید توانایی متخصصان شبکه که در زمینه هایی از قبیل پیاده سازیِ زیرساخت، پیکربندی، مدیریت و عیب یابی سیستم عامل های امنیتی مبتنی بر Junos فعالیت دارند، برگزار می شود. افرادی که از این دوره با موفقیت عبور کنند، قادر خواهند بود که با اعمال قوانین پیچیده و توانایی پیشگیری از حملات، شبکه های بسیار وسیعی با قابلیت های HA و ویژگی های IPS را مدیریت کنند.
Objectives
After successfully completing this course, you should:
- Be better prepared for success in taking the actual JNCIE-SEC exam.
- Be well-versed in exam topics, environment, and conditions.
Course Contents
Day 1
Chapter 1: Course Introduction
Chapter 2: Exam Strategies
- Prior to the Exam
- Exam Day
- After the Exam
Chapter 3: Infrastructure Concepts
- Section Topics
- System Tasks
- Zones
- Issues and Tips
- Infrastructure and Zones Lab
Chapter 4: Building Clusters
- Setting Up Clustering
- Redundancy Groups and Reth Groups
- Failovers
- Issues and Tips
- Creating Clusters Lab
Day 2
Chapter 5: Security Policies
- Security Policies
- ALGs
- Schedulers
- Firewall Authentication
- Bypass Flow Forwarding
- Logging
- Issues and Tips
- Building Security Policies Lab
Chapter 6: IPsec VPNs
- Overview of VPN Configuration
- IKE Proposals, Policies, and Gateways
- IPsec Proposals, Policies, and Gateways
- Route-Based, Dynamic, and Certificate-Based VPNs
- Traceoptions
- Issues and Tips
- Building IPsec VPNs Lab
Day 3
Chapter 7: Network Address Translation
- Implementation of NAT
- Source NAT
- Destination NAT
- Static NAT
- Overlapping IP Addresses
- Verification Commands and Common Issues
- Network Address Translation Lab
Chapter 8: Attack Prevention
- Overview of Attack Prevention
- IDP
- Additional Prevention Capabilities
- Issues and Tips
- Attack Prevention Lab
Day 4
Chapter 9: Unified Threat Management and Screen Options
- Overview of UTM
- Web Filtering
- Anti-Virus
- Screen Options
- UTM and Screen Options Lab
Chapter 10: Extended Implementation Concepts
- Transparent Mode
- Filter-Based Forwarding
- Extended Implementations Lab
Day 5
- JNCIE-SEC Full Lab Simulation
جمع بندی
در مستند ارائه شده انواع مدارکِ لازم جهت گذراندن دوره های جونیپر به همراه دوره های مورد نیاز و ساعات هر دوره برای یک مدرک خاص ارائه گشته است. با توجه به اینکه بیش از ۵۰% مطالب این دوره به صورت مفاهیم امنیت شبکه می باشد، دانشجویان این دوره با کسب اطلاعات در این دوره امکان طراحی و ارائه راهکار های امنیت شبکه برای سایر برند ها را نیز قادر خواهند بود.














