Rayan Nik Tajhiz Company
What is the Oracle database firewall?
Oracle Company has provided its first firewall, called Oracle Database Firewall, for the safe use of databases to preserve valuable systems against attacks and any destruc
tive operations.
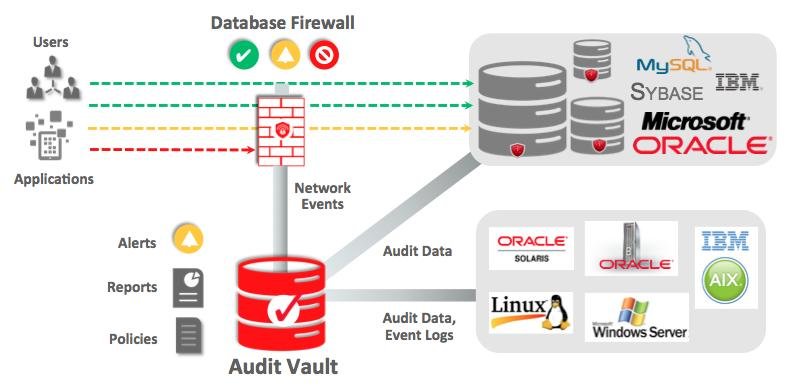
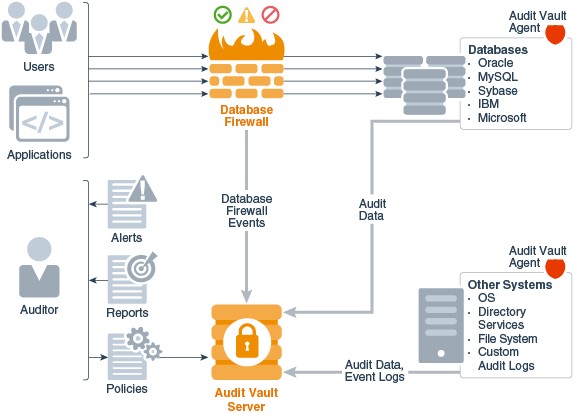
By implementing the Oracle database firewall, as the first agent in database protection, performing people and database traffic can be monitored in real-time and operational environment. The oracle database firewalls monitor any attempt to destroy and infiltrate the systems. It also can diagnose any attack against SQL. Note that the database firewall is designed in such a way as to prevent both internal and external attacks on the database. Regarding the increasing complexity of the type of attacks, the powerful design of these databases is getting essential. So, a unique technology called “SQL grammar” is used in database firewalls to identify attacks on databases, classify hacker attempts, and explore their behaviors.

What Oracle Database Firewall can do?
The Oracle Database Firewall can allocate special authority to a specific group of users in order to use a resource or even block those outside the group who want to access the resources.
Another is to restrict suspicious and malicious queries, which is the way to penetrate and collapse the database. The other benefit of the Oracle database firewall is its reporting and warning feature. It should be noted that besides prevention, this tool can report and inform under the definable and suspicious cases.
Key features of Oracle Database Firewall
● Flexibility in implementation, including blocking and monitoring models,
● Policies based on whitelists, blacklists, and exception lists
● Very flexible architecture for enterprise applications
● Pre-made and customizable reports
● Urgent security alerts
● Supporting all Oracle, MySQL, Microsoft SQL Server, Sybase, and IBM DB2 databases
● Supporting Oracle TDE security feature
A whitelist is a group of confirmed SQL statements that the firewall expects to see them. The blacklist contains templates, tables, users, and SQL statements that may not be sent to the database. The rules of the exceptions list provide more flexibility, which can replace rules based on whitelist and blacklist.
Note that these rules can be applied based on attributes such as the SQL category, time, program, user, and IP address. In this way, Oracle Database Firewall can log requests, display a warning, and either block incoming SQL commands or replace them with a safe SQL command.
By analyzing the SQL statements sent to the database, Oracle Database Firewall evaluates its meaning and then applies the proper security rules.
Grammatical classification and profiling based on session factors are powerful ways to track database access. The security structure of Oracle Database Firewall can identify any change in normal behavior, such as SQL Injection attacks (generating malicious data on the database) on programs, as well as can prevent attacks before reaching the database.
This highly accurate approach prepares a much higher protection than the earlier generation of database monitoring technologies made based on detecting signatures of known security threats.
How to implement the Oracle database firewall?
Among the different firewalls created for the database, implementing the Oracle database firewall costs less than the others, but it needs high technical knowledge to implement and install regarding the security policies of organizations. Rayan Nik Tajhiz Company can implement such a firewall with its experienced experts. Organizations can call +982188209267 Extension 222 to see its technical demo as well as how to implement it.

